You may think that you have good password security. More likely, you are like most people who re-use the same password for many accounts, don’t change it often enough and use your pet’s name or some other easy to find information that makes break in easy.
Face it, we are lazy, lax and don’t understand security and privacy. Nor do we understand the nature of identity theft until you are a victim.
So, unless your are fastidious about changing with complete randomness and creativeness, fugetaboutit, you’re toast…..here’s why.
THE BACKGROUND
From Wired:
It’s not a well-kept secret, either. Just a simple string of characters—maybe six of them if you’re careless, 16 if you’re cautious—that can reveal everything about you.
Your email. Your bank account. Your address and credit card number. Photos of your kids or, worse, of yourself, naked. The precise location where you’re sitting right now as you read these words. Since the dawn of the information age, we’ve bought into the idea that a password, so long as it’s elaborate enough, is an adequate means of protecting all this precious data. But in 2012 that’s a fallacy, a fantasy, an outdated sales pitch. And anyone who still mouths it is a sucker—or someone who takes you for one.
No matter how complex, no matter how unique, your passwords can no longer protect you.
Look around. Leaks and dumps—hackers breaking into computer systems and releasing lists of usernames and passwords on the open web—are now regular occurrences. The way we daisy-chain accounts, with our email address doubling as a universal username, creates a single point of failure that can be exploited with devastating results. Thanks to an explosion of personal information being stored in the cloud, tricking customer service agents into resetting passwords has never been easier. All a hacker has to do is use personal information that’s publicly available on one service to gain entry into another.
This summer, hackers destroyed my entire digital life in the span of an hour. My Apple, Twitter, and Gmail passwords were all robust—seven, 10, and 19 characters, respectively, all alphanumeric, some with symbols thrown in as well—but the three accounts were linked, so once the hackers had conned their way into one, they had them all. They really just wanted my Twitter handle: @mat. As a three-letter username, it’s considered prestigious. And to delay me from getting it back, they used my Apple account to wipe every one of my devices, my iPhone and iPad and MacBook, deleting all my messages and documents and every picture I’d ever taken of my 18-month-old daughter.
The age of the password is over. We just haven’t realized it yet.
Since that awful day, I’ve devoted myself to researching the world of online security. And what I have found is utterly terrifying. Our digital lives are simply too easy to crack. Imagine that I want to get into your email. Let’s say you’re on AOL. All I need to do is go to the website and supply your name plus maybe the city you were born in, info that’s easy to find in the age of Google. With that, AOL gives me a password reset, and I can log in as you.
First thing I do? Search for the word “bank” to figure out where you do your online banking. I go there and click on the Forgot Password? link. I get the password reset and log in to your account, which I control. Now I own your checking account as well as your email.
This summer I learned how to get into, well, everything. With two minutes and $4 to spend at a sketchy foreign website, I could report back with your credit card, phone, and Social Security numbers and your home address. Allow me five minutes more and I could be inside your accounts for, say, Amazon, Best Buy, Hulu, Microsoft, and Netflix. With yet 10 more, I could take over your AT&T, Comcast, and Verizon. Give me 20—total—and I own your PayPal. Some of those security holes are plugged now. But not all, and new ones are discovered every day.
The common weakness in these hacks is the password. It’s an artifact from a time when our computers were not hyper-connected. Today, nothing you do, no precaution you take, no long or random string of characters can stop a truly dedicated and devious individual from cracking your account. The age of the password has come to an end; we just haven’t realized it yet.
Passwords are as old as civilization. And for as long as they’ve existed, people have been breaking them.
In 413 BC, at the height of the Peloponnesian War, the Athenian general Demosthenes landed in Sicily with 5,000 soldiers to assist in the attack on Syracusae. Things were looking good for the Greeks. Syracusae, a key ally of Sparta, seemed sure to fall.
But during a chaotic nighttime battle at Epipole, Demosthenes’ forces were scattered, and while attempting to regroup they began calling out their watchword, a prearranged term that would identify soldiers as friendly. The Syracusans picked up on the code and passed it quietly through their ranks. At times when the Greeks looked too formidable, the watchword allowed their opponents to pose as allies. Employing this ruse, the undermatched Syracusans decimated the invaders, and when the sun rose, their cavalry mopped up the rest. It was a turning point in the war.
The first computers to use passwords were likely those in MIT’s Compatible Time-Sharing System, developed in 1961. To limit the time any one user could spend on the system, CTSS used a login to ration access. It only took until 1962 when a PhD student named Allan Scherr, wanting more than his four-hour allotment, defeated the login with a simple hack: He located the file containing the passwords and printed out all of them. After that, he got as much time as he wanted.
During the formative years of the web, as we all went online, passwords worked pretty well. This was due largely to how little data they actually needed to protect. Our passwords were limited to a handful of applications: an ISP for email and maybe an ecommerce site or two. Because almost no personal information was in the cloud—the cloud was barely a wisp at that point—there was little payoff for breaking into an individual’s accounts; the serious hackers were still going after big corporate systems.
So we were lulled into complacency. Email addresses morphed into a sort of universal login, serving as our username just about everywhere. This practice persisted even as the number of accounts—the number of failure points—grew exponentially. Web-based email was the gateway to a new slate of cloud apps. We began banking in the cloud, tracking our finances in the cloud, and doing our taxes in the cloud. We stashed our photos, our documents, our data in the cloud.
Eventually, as the number of epic hacks increased, we started to lean on a curious psychological crutch: the notion of the “strong” password. It’s the compromise that growing web companies came up with to keep people signing up and entrusting data to their sites. It’s the Band-Aid that’s now being washed away in a river of blood.
WHERE AND WHEN IT BEGAN (SORT OF)
No one can be sure except that since passwords were first used, there were bad guys trying to hack into them. Here is an exposition of how it became an epidemic:
In 2009, a minor gaming website called Rockyou.com was hacked; although you’ve probably never heard of the site, the hack has probably affected you or someone you know. Almost every genuine hack over the last three years can be traced back to the Rockyou leak.
The reason it was so significant is it totally changed the way hackers do business. Before Rockyou, hackers had to build word lists of potential passwords using traditional dictionaries; the 14 million or so Rockyou passwords provided an instant database showing how people actually construct their passwords.
We’re all familiar with the hoops passwords make us jump through – requiring both letters and numbers, the use of upper-case and lower-case letters, a minimum number of characters, and the use of punctuation. Of course,we’re all human, so we want passwords to be easy to remember while fulfilling these arcane rules.
The list leaked from RockYou confirmed our grammatical bias: upper case letters tend to start words, while special characters or numbers come at the end. One of the most common ways to combine letters and numbers memorably was to add names & dates together – so Patton1945 or Napoleon1815 were common, for example.
Publicly available data makes this even easier; for example, databases are available containing the name of every Facebook user. These, when combined with every 4-digit number combination and a dictionary list of common words will break as many as 40 per cent of internet users’ accounts within minutes. This creates an even greater problem, as many people reuse passwords, meaning one crack can compromise multiple accounts.
Most people have multiple different internet accounts; collecting data and monitoring user activity through these accounts is at the core of many websites’ business models. The temptation to reuse important passwords for trivial sites that require a sign-in, like price comparison sites, restaurant bookers, dating sites or online shops, is almost irresistible. Of course, many of these sites are far from secure.
The Rockyou leak started a chain reaction; a huge number of sites have been hacked since, releasing even more password data. Equally, technology has advanced enormously. The sort of PC you can buy in Currys can attempt 8.2 million password combinations per second. Cryptographic feats that were the stuff of legend in the Second World War could be done on your iPhone; the sort of 16-digit passcodes thought uncrackable during the Cold War are now within the reach of cracking by skilled hackers with low budgets. Goodness only knows what state-sponsored outfits in the US or China can do.
If you look in the lists of passwords and usernames leaked online, it’s fairly easy to find yourself; with the huge amount of websites we sign up to these days, it’s almost inevitable that at least one of the sites where you have an accounts has been hacked in the last two years. I was able to find my own cracked username and password (taken from a hacked wargaming forum) with a little diligent searching. The biggest damage that could be done to me from that leak is losing control of my forum account; if I’d reused that password elsewhere, it could have been catastrophic.
Of course, each character you add to your password ramps up the time it takes to crack; adding even one letter can take crack time from hours to days, putting you into the category of not “unbreakable” – I doubt such a thing exists – but simply not worth the hassle.
The current best advice is to have passwords composed of 20 characters, with no real words, and your gobbledegook has to include upper and lower case letters, symbols, numbers and punctuation, all randomly scattered through the word. On top of that, you need to have a different password for every site you use and change your password for all of them every three months.

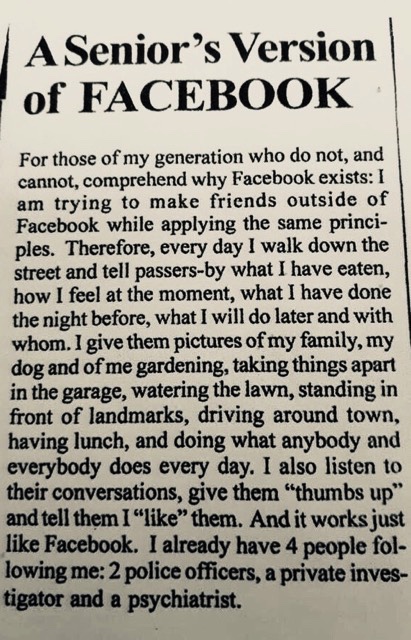
 Scroll down a few posts and you’ll see other articles I’ve posted that talk about Social Media ruining people’s lives. It’s their outside daring you to compare, unfortunately to your inside.
Scroll down a few posts and you’ll see other articles I’ve posted that talk about Social Media ruining people’s lives. It’s their outside daring you to compare, unfortunately to your inside.